[4 mins read]
Ransomware– a term that strikes fear in the heart of individuals and businesses. In simple terms, ransomware is malicious software designed to lock files on a victim’s computer or network, rendering them inaccessible until a ransom is paid. This encryption process prevents the victim from accessing their devices or any of their files without the decryption key held by the attacker.
Imagine someone locking up your house, leaving you unable to access your belongings. The person who locked your house then demands a ransom for you to regain access to your items. Scary, isn’t it?
Contrary to popular belief, Small and Medium Enterprises (SMEs) are just as vulnerable to ransomware attacks as larger organizations. In fact, SMEs have become increasingly popular targets for malicious actors over the years. Here are some common consequences:
- Operational downtime
- Massive financial losses can cripple a company’s budget
- Irreparable damage to reputation and customer trust
- Legal penalties for failing to protect sensitive data
- High cost of restoring and securing systems
The impact of a ransomware attack can be devastating, and not all businesses can recover from it. According to a report published earlier this year, the average demanded ransom from attackers in 2024 was over S$5.8 million (US$4,321,880). Of all the ransomware demands, about 63% demanded more than S$1.3 million (US$1 million), and about 30% demanded more than S$6.7 million (US$5 million). It is important to note that these ransom payments are just part of the cost of recovering from a ransomware attack. There is no guarantee that the data can be recovered even after the payment, hence, businesses are advised not to pay the ransom.
In 2023, the average cost to recover from a ransomware attack was reported at about S$2.5 million (US$1.82 million). However, in 2024, this number almost doubled, reaching about S$3.7 million (US$2.73 million). The recovery time for a ransomware attack has also been increasing over the years.
In most scenarios, ransomware attackers may have duplicates of your data, which can be sold or leaked, causing further damage. This adds to the complexity and severity of ransomware attacks, highlighting the importance of ransomware prevention solutions and incident response plans.
Ransomware Recovery Process
Confronting a ransomware attack can be daunting, however, the recovery process is not impossible. To simplify this process, here are four steps to guide you through the ransomware recovery process:
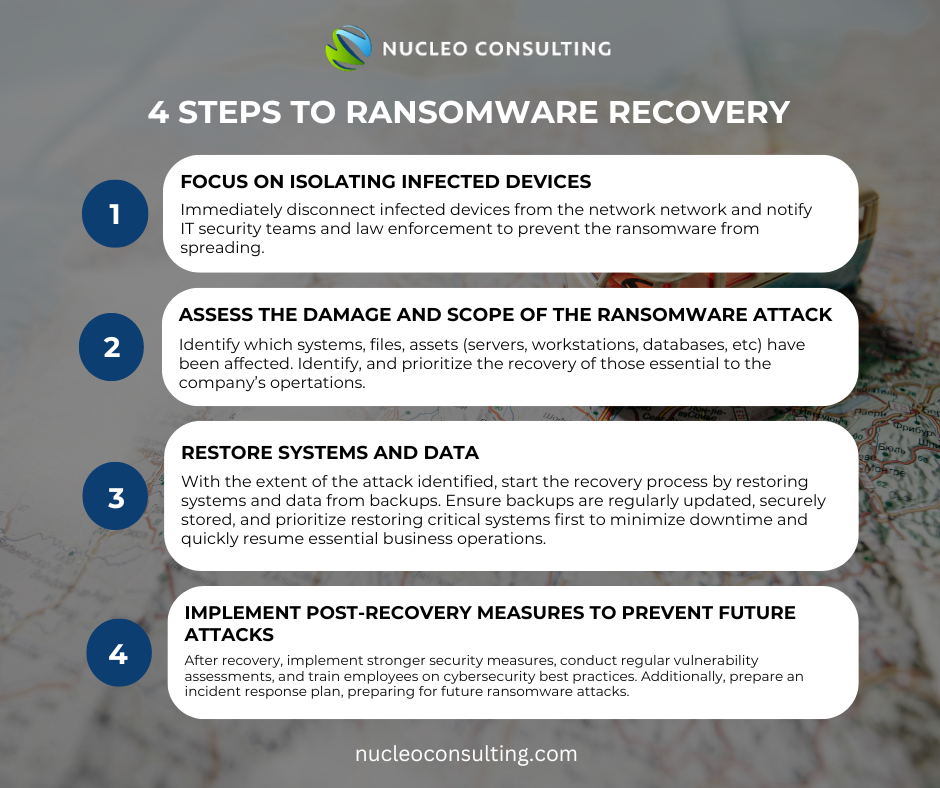
Step 1: Focus on isolating infected devices
Immediate action is crucial when facing a ransomware attack. Upon detection, the first response should be focused on isolating the infected devices and networks to prevent the further spread of the ransomware.
Alerting appropriate authorities is crucial for containing the breach and gathering essential information for the investigation. These authorities include the Singapore Police Force (SPF), the Personal Data Protection Commission (PDPC), the Cyber Security Agency of Singapore (CSA), as well as IT security and law enforcement agencies. By informing authorities, you would protect yourself and others from future similar breaches.
Step 2: Assess the Damage and Scope of the ransomware attack
After alerting the authorities, assess the extent of the damage. Identify which systems and files have been affected by the ransomware attack and the full extent of the breach. Following this, it’s crucial to determine the scope of the attack to prioritize recovery effectively. Identify affected assets such as servers, workstations, and databases to gauge the impact. A clear understanding of both the damage and scope allows for targeted and efficient recovery efforts, minimizing downtime and business impact. Transparent communication with stakeholders is essential throughout this process.
Step 3: Restore Systems and Data
With the scope of the attack determined, initiate the recovery process. This typically involves restoring systems and data from backup.
Regularly update and securely store backups to ensure successful recovery. Ensure that the backup is not accessible to the attackers to prevent further manipulation. According to the scope, prioritize the backup of critical systems and data to minimize downtime and restore essential business operations as quickly as possible.
Step 4: Implement Post-Recovery Measures to prevent future attacks
Once the recovery process is completed, it’s crucial to implement post-recovery measures to prevent future attacks. This includes strengthening security measures, such as implementing multi-layered defenses, conducting regular vulnerability assessments, pen testing, and training employees on cybersecurity best practices.
Additionally, businesses should prioritize incident response planning and preparedness. Having a well-defined incident response plan in place can help mitigate the impact of future ransomware attacks and minimize downtime.
Engaging with Ransomware Operators
Engaging with ransomware operators and ransom payments are strongly discouraged. Paying the ransom offers no assurance that your files will be decrypted. Moreover, it encourages cybercriminals to continue their illegal activities and target more people. Making a payment does not ensure that your data will not be exposed by attackers.
Additionally, paying a ransom may signal to threat ransomware operators that your business is an easy target, increasing the likelihood of future attacks.
Alternatively, businesses can explore other avenues for recovering encrypted data, such as seeking advice and assistance from cybersecurity experts.
Conclusion
Ransomware poses a significant threat to individuals and businesses, but recovery is possible with the right strategies in place. By understanding the ransomware recovery process, exploring alternatives to engaging with ransomware operators, and implementing post-recovery measures, businesses can mitigate the risk of future attacks and protect their data and assets.
It is essential to remain vigilant and proactive in the face of evolving cyber threats. By prioritising cybersecurity awareness and preparedness, organizations can safeguard themselves against the devastating impact of ransomware attacks. Remember, prevention is always better than cure when it comes to ransomware.
Ransomware | IT Tips | Cybersecurity | Cyber Attack | Data Breach | Cyber Threats | Pentesting | VAPT | SME | Hackers | Malware