With the ever-growing technologies, cyber crimes has also been increasing significantly in the recent years. With the Covid-19 situation being one of the key factors for the increment, the cases of cyber crimes rapidly increased from 9,349 cases in year 2019 to more than 16,000 cases in year 2020, which is equivalent to 43% of the overall crimes in Singapore.
‘ Money is the root of all evil ‘
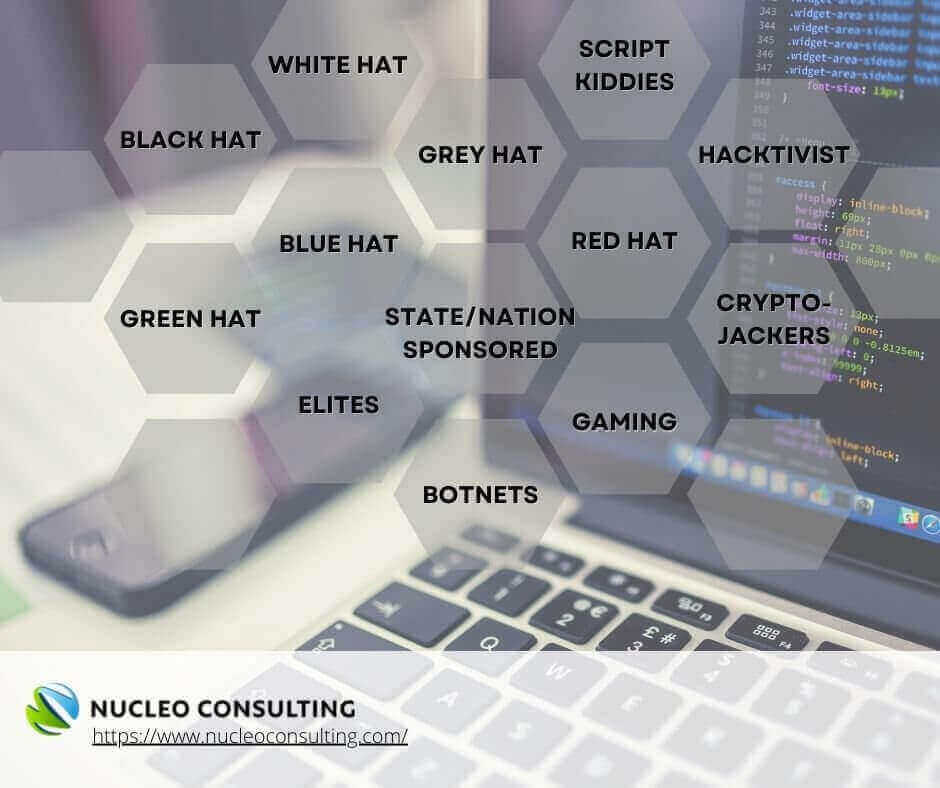
We have all heard of this phrase, but in fact, money is not all the hackers are looking for. Lets take a look at the different types of hackers and find out what attracts them.
(Source: Panda Security)
BLACK HAT HACKERS
These hackers may be the closest to what you had expected from a typical hacker. These black hat hackers are global cyber criminals who are very difficult to stop. Equipped with advanced cyber security knowledge and skills, their attacks are destructive to both businesses and individuals. They are often attracted by profit from data breaches, which means that businesses are at the most risks. Beware of the details shared via emails and messages! It’s what they’re attracted to!
WHITE HAT HACKERS
The white hat hackers are people with different motives than that of a Black Hat hacker. They use their advanced technological skills and knowledge to the advantage of governments or businesses. The white hat hackers are authorized hackers for the purpose of identifying vulnerability in the cyber security systems of those who hires them.
GREY HAT HACKERS
These are cyber security experts who hacks for fun. The grey hat hackers are attracted to the excitement of finding the loopholes in your computers and systems, and sometimes, without the owner’s permission to do so! Although they might not try to cause any harm, but these hackers are not to be taken lightly too!
GREEN HAT HACKERS
Refers to a hacker who is new to hacking. The green hat hackers are mainly attracted to the opportunity to learn and gain knowledge of hacking. Beware! Being new doesn’t mean no damages!
BLUE HAT HACKERS
These are hackers hired by organizations to put their network system or software to the test before launch. The Blue Hat hackers are mainly attracted to the loopholes and vulnerabilities in the system/ software of the organization who hired them.
RED HAT HACKERS
The red hat hackers are hired by the government agencies to assist to identify weakness in their cyber security systems. Their job is to identify and hunt down the black hat hackers and are attracted to locate and destroy the black hat hackers!
SCRIPT KIDDIES
This refers to the less experienced hackers who uses malware created by other hackers for attacking. The main motive of the script kiddies is to create disruptions and are attracted to businesses without proper cyber security in their network/systems.
STATE/NATION SPONSORED HACKERS
This refers to hackers who are hired by the government agencies to gain access to another nation’s systems. These state/nation sponsored hackers use their advanced cybersecurity skills and knowledge to obtain confidential information from other countries such as preparation of an attack/threat, and to keep a pulse on sensitive situations that could lead to any other threats in the future.
MALICIOUS INSIDER HACKERS
Also known as the Whistleblower hackers, this refers to individuals who are employed by the organization but cyber attacked the company they worked for. They can be existing or former employees, contractors, or associates who has access to the company’s systems, and may be attacking due to personal grudges, or exposing any illegal activities that they have found.
HACKTIVISTS
These are hackers who hacks into government’s network/systems as a form of protest, or, to obtain sensitive information to be used for political purposes. Needless to say, they are attracted to sensitive information that can be used for political/ social purposes.
ELITE HACKERS
Top of the pyramid, they have the best skills and knowledge in their field. The elite hackers are generally the ones who implements new attacking methods and are attracted to perform attacks on large profitable organizations and wealthy individuals.
CRYPTOJACKERS
These hackers are people who are attracted to the benefits of cryptocurrency mining, but are not keen to pay huge expenses for mining equipment or bills incurred. Cryptojackers hack into other users’ devices to mine for cryptocurrency and is often difficult to trace.
BOTNETS
Derived from the word “robots” and “network”, botnet refers to the tool used for mass cyber attacks (data theft, spreading of malware, disrupting the servers, etc). It uses your device to spread and scam others, which causes disruptions. They generally target Wi-Fi connected devices such as cameras, IoT devices, routers and so on. Botnet hackers are generally attracted to disrupt high volume of systems.
With all the different types of hackers listed above, we can conclude that not every hacker is attracted to profit. Apart from those who are hired and authorized to hack in views on checking for loopholes in the organizations’ cyber security systems, any damage will be destructive.
As technology advances, the techniques used to prey on the victims become more innovative as well. This is why you should always check that the software installed on your devices are up-to-date, especially those for antivirus, firewall, or windows updates. These updates may contain bug fixes, updates of new features, and is crucial for the optimal performance of these software.
No matter how big or small your business is, all cyber threats are not to be taken lightly. Your cyber security defenses must be in place, so that you can focus on your businesses.
As we always say, It’s always better to be cyber-safe, than sorry!
cyber attack | cyber safety | importance of cyber security | hackers | cyber security