[3 mins read]
We live in a world of ever-changing technologies, where mobile devices aren’t just for phone calls anymore. Smartphones have also been evolving to cater to our daily needs. From communications to navigation, reservations to shopping, as long as our smartphones are connected to the internet, there are really no boundaries to what we can achieve with this great invention. Users can leave their computers on their desks but often carries their smartphones everywhere they go.
Smartphone and internet connection- a powerful combination of technologies we can’t live without. The speed of our internet connection, the information available on the internet, and the introduction of the Internet of Things (IoT)/ smart products have proven that technology is advancing, rapidly.
Unfortunately, technology is a double-edged sword. Cyber threats have also tagged along with the waves of new technologies, causing more destructive damages. Cyber-attacks are not just destructive for businesses, they are destructive for everyone. No matter work or leisure, cyber safety for you and your loved ones should not be overlooked. Here are some tips to keep your device cyber safe:
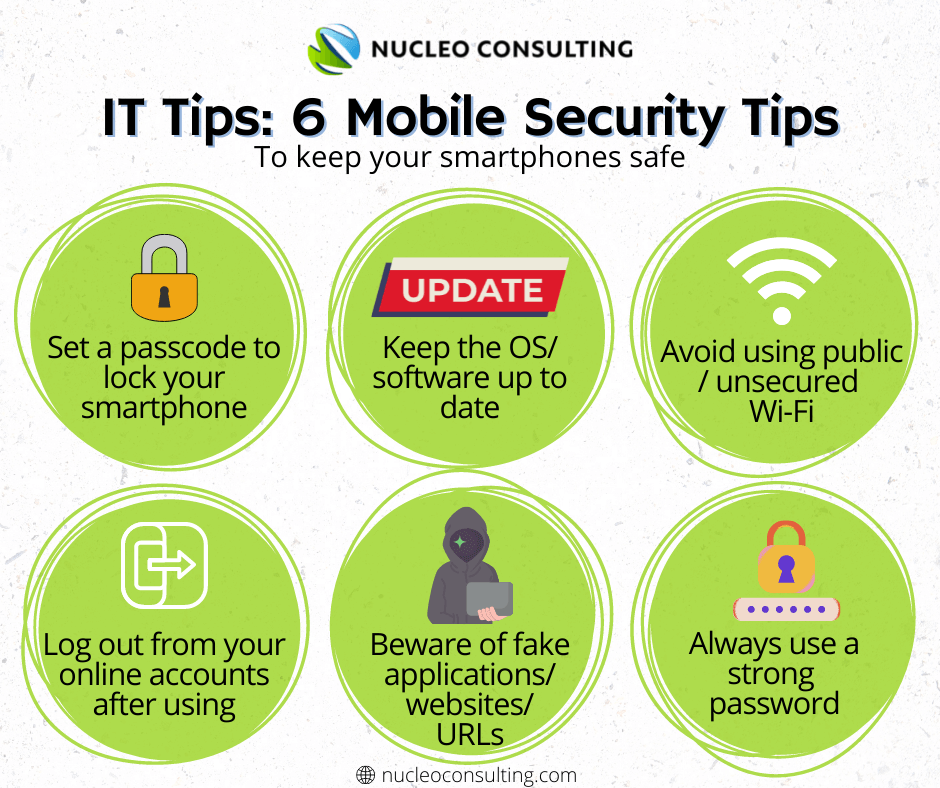
1. Lock it up
Like our homes, our smartphones often contain important things that we do not want to share with others. Keeping your phone locked is the first step to prevent unauthorized access to your contact lists, photos, emails, and other sensitive/ personal information you may have stored in your phone!
2. Keep the software up to date
Smartphones often have mobile operating system updates to improve their performance, new features, or bug fixes. Ensuring that the operating system of your phone and the software for all the mobile applications are up to date so that its performance and security features are optimized.
3. Secured Wi-Fi
Free public Wi-Fi? Think again. These are usually unsecured and can be hacked by IT experts. Do not use unsecured connections to access your online accounts such as social media, emails, or banking accounts which may contain your personal information or sensitive data!
4. Logging out
Log out from your online accounts once you have finished using them. Not all applications have the feature to log out automatically once you have stopped using it. Logging out of your online accounts after use will ensure the safety of these accounts if your phone gets stolen and the thieves gained access to your phone.
Take a look at your mobile applications such as social media, e-commerce/ shopping, messenger, and emails. How many of these application does not require additional log-in after you have unlocked your phones?
5. Mobile Applications/ Websites
Yes, there are fake applications and websites out there, created by cybercriminals to look identical to an official mobile application or a website. These malicious applications and websites are often used to trick victims and to obtain sensitive/personal information such as login credentials.
Do not click on any suspicious URLs/ links even if it is sent by someone you know. Do not respond to SMS, WhatsApp, emails, or phone calls that are from unknown sources. And be sure to download mobile applications from the official App Store/ Play Store and delete applications that are no longer required.
6. Strong Passwords
Passwords are the first security measures for your devices and accounts. A device or an account without a password is dangerously easy for cybercriminals to gain access to your personal data or sensitive information.
Create a strong password by ensuring that it does not contain personal information such as birthdates, anniversary dates, or phone numbers. Include a mixture of upper-case and lower-case alphabets and include symbols to strengthen your passwords. Do not use the same passwords for all your accounts and activate the multi-factor authentication whenever possible!